Introduction
While there is an enormous volume of information both in books and on-line with respect to networking they all seem to suffer from the same problems, start beyond basic level; try to encompass too many areas of technology and are generally difficult to read.
A network is simply a mechanism which allows two or more systems to communicate and defines the rules to enable communication to take place. For example, think of the 'phone network. Whether mobile or landline you take a device that is capable of connecting to the network (BT, Virgin etc.) and, once connected, you can communicate with other 'phones. As the networks are connected to each other you can communicate with 'phones on other networks too.
There could be many reasons why you would want to gain an understanding of networks including career development or hobby interest. For example, a lot of technology such as TV and audio equipment comes network-enabled. Many TVs can connect to the Internet or media servers on your home network. Also, there is your Internet connection itself of course.
All of these products use a form of Ethernet as their networking technology whether by wired connection or wireless so a good place to start may be with Ethernet as that is what most people will be familiar with. As it's used extensively in both the home and place of work it should be relevant to most users.
Rather than diving in to the techy stuff first it may be good to have a look at the history of Ethernet as it puts things in perspective.
History of Ethernet
Networking today is much different to the original concept which revolved mainly around connecting computers together that were generally quite close to one another and connecting remote devices such as 'dumb' terminals and printers. Consequently, networking has evolved quite a bit over the decades as computer systems have become more widespread and the technology in desktop, laptop and mobile systems has become more refined. Even so, a lot of the networking technology used today is an evolution of that first used all those decades ago.
Although you can trace the history of networking back as far as the forties, networking as we would recognise it really starts with the development of Ethernet at Xerox Parc around 1974-75. It was inspired by ALOHAnet which was an early wireless network used to link the various parts of the University of Hawaii to the central computers. Wireless because the university spreads over several islands. ALOHAnet was, essentially, packet radio which just means that whatever data you want to send is chopped up into small segments (packets) and sent a packet at a time.

The challenge at Xerox Parc was to develop a means of using cabling in a similar manner. Effectively, Ethernet is an evolution of packet radio with each device transmitting packets but over cable rather than the airwaves. The end result was Ethernet adapters which were miniature radio transmitter/receivers connected together using coaxial cable coupled with software that defined the rules and allowed networking to take place.
Ethernet Rules
Ethernet rules are like manners for computers! Imagine being out for a meal with friends and you have something you'd like to say but someone else is talking. Normally, you'd wait until they'd finished or both messages would likely get lost in all the clutter. Networks have similar problems, if two or more devices try to send at the same time the messages can get too cluttered for either to be understood.
Many mechanisms exist to handle this issue but the most basic is CSMA/CD (Carrier Sense, Multiple Access/Collision Detect) which is harder to say than it is to understand. Effectively it breaks down into three parts, Carrier Sense means check whether another device is sending before sending yourself. Multiple Access just means many devices can use the same piece of cable and, because of this, collisions may occur so listen while sending (Collision Detect). A collision is simply the result of two or more devices sending at the same time which results in the blocks of data (packets) being damaged.
Sending devices listen while sending and if what they hear is different to what they sent then a collision is assumed. At this point both stop sending and transmit a 'jam' signal to indicate that the cable has a 'traffic jam' and they wait for a random period before trying to send again.
Modern equipment does use other mechanisms but still 'falls back' to CSMA/CD if all else fails. One such mechanism is the use of a switch which separates all the devices from each other as each device has its own port on the switch. Collisions are not necessarily completely eliminated but are considerably reduced. This is because the device and the port on the switch are in the same 'collision domain' i.e. they could send simultaneously. However, if device and switch can run full-duplex (both send and receive at the same time) no collisions could occur.
Other rules define things like how long the cables can be, what type(s) are used and the connectors that are allowed. Having these rules means that if you buy a specific Ethernet cable then, barring manufacturing defects, it should just work. Similar to buying a new landline 'phone, it comes with a standard plug to fit a standard BT socket.
Cable lengths are important because signals degrade over distance so you need to ensure that the signal is sufficently strong to be readable by the receiver. You can place amplifiers (known as repeaters) at strategic points but while amplifiers do make the signal stronger they also add noise which is hard to separate from the data. In addition, repeaters introduce transmission delays. Network software will assume a transmission error if the delays are too great. Consequently, maximum cable lengths are specified in the rules as are the number of repeaters allowed.
These rules are defined in specifications developed and published by IEEE and in the OSI 7-layer model which describes what takes place at the different stages of networking and how the stages communicate. For example, connectors, cable types, repeaters/hubs etc. are confined to Layer 1 which is the most basic level of the network.

At this point we're only interested in the fact that it's a conceptual model which helps you to visualise what happens; it comprises two main sections, the Application Set is where stuff like browsers live, this section determines what should be sent and where to, and; the Transport Set. The Transport Set determines how stuff gets sent and right at the bottom is the Physical Layer, Layer 1, where stuff gets put onto the cable.
Simply put, Layer 1 moves datagrams around. A datagram is a generic name for something that moves around the network with data in it. Think about it as being like something you put in the postbox, it can't be too big as it won't go through the slot/letterbox (about 1500 bytes is typical) and it has the address to send it to, the address it came from and whatever you're sending (the payload).
Here's a typical example.
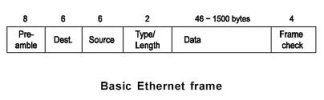
The preamble is like waving a flag saying I'm sending you something. Destination and Source are the addresses it's going to and coming from respectively. Type/Length is usually used to indicate how big the Data part (or payload) is while the Frame Check is used at the receiving end to help determine if everything arrived correctly. You can imagine this frame or datagram as travelling along the wire with the preamble first.
Now, at this level we are talking about hardware or MAC addresses, Layer 1 doesn't know anything about IP addresses or anything fancy like that. The hardware (or MAC) address is programmed into the Ethernet adaptor when it is manufactured. Each manufacturer has blocks of MAC addresses assigned to it for use on its own adaptors. The MAC address of my computer is:
00:13:72:ca:40:6d
You can find out yours by running 'ipconfig' in a Windows command prompt (or 'ifconfig' in a Linux terminal). It's a 12-digit Hexadecimal number (base 16, so digits go from 0-15 i.e. 0,1,2,3,4,5,6,7,8,9,a,b,c,d,e,f) and plugging this number into an on-line MAC address checker (MAC_Find: Vendor/Ethernet/Bluetooth MAC Address Lookup and Search) reveals mine is one of a block assigned to Dell. So, at this simplest level of networking, Layer 1, information can only be sent to other devices on your home network. To send something to the Internet requires that the address of the Internet device be placed in the payload part of the datagram which is then sent to whatever you connect to the Internet with.
What Layer 1 DOESN'T do is define what's IN the payload part of the datagram, that's done elsewhere, like a program. As an example, when you Google something it's the web browser that decides what to send and where, the networking software decides how to send it and when it gets all the way down to Layer 1 it gets transmitted on the cable.
So, when people talk about a Layer 1 activity or device you know they mean connectors, cables, repeaters, hubs etc. You should also be aware that some words and phrases in networking are used interchangably but mean different things. When I refer to a 'hub' I'm talking about a piece of networking equipment used to 'repeat' an incoming signal onto one or more other outgoing cable segments. When Virgin talk about a hub they mean the piece of kit they send you to connect to their broadband service. It's not really a 'hub', it's a router/firewall/switch and combined modem. Not quite the same thing!
While there is an enormous volume of information both in books and on-line with respect to networking they all seem to suffer from the same problems, start beyond basic level; try to encompass too many areas of technology and are generally difficult to read.
A network is simply a mechanism which allows two or more systems to communicate and defines the rules to enable communication to take place. For example, think of the 'phone network. Whether mobile or landline you take a device that is capable of connecting to the network (BT, Virgin etc.) and, once connected, you can communicate with other 'phones. As the networks are connected to each other you can communicate with 'phones on other networks too.
There could be many reasons why you would want to gain an understanding of networks including career development or hobby interest. For example, a lot of technology such as TV and audio equipment comes network-enabled. Many TVs can connect to the Internet or media servers on your home network. Also, there is your Internet connection itself of course.
All of these products use a form of Ethernet as their networking technology whether by wired connection or wireless so a good place to start may be with Ethernet as that is what most people will be familiar with. As it's used extensively in both the home and place of work it should be relevant to most users.
Rather than diving in to the techy stuff first it may be good to have a look at the history of Ethernet as it puts things in perspective.
History of Ethernet
Networking today is much different to the original concept which revolved mainly around connecting computers together that were generally quite close to one another and connecting remote devices such as 'dumb' terminals and printers. Consequently, networking has evolved quite a bit over the decades as computer systems have become more widespread and the technology in desktop, laptop and mobile systems has become more refined. Even so, a lot of the networking technology used today is an evolution of that first used all those decades ago.
Although you can trace the history of networking back as far as the forties, networking as we would recognise it really starts with the development of Ethernet at Xerox Parc around 1974-75. It was inspired by ALOHAnet which was an early wireless network used to link the various parts of the University of Hawaii to the central computers. Wireless because the university spreads over several islands. ALOHAnet was, essentially, packet radio which just means that whatever data you want to send is chopped up into small segments (packets) and sent a packet at a time.

The challenge at Xerox Parc was to develop a means of using cabling in a similar manner. Effectively, Ethernet is an evolution of packet radio with each device transmitting packets but over cable rather than the airwaves. The end result was Ethernet adapters which were miniature radio transmitter/receivers connected together using coaxial cable coupled with software that defined the rules and allowed networking to take place.
Ethernet Rules
Ethernet rules are like manners for computers! Imagine being out for a meal with friends and you have something you'd like to say but someone else is talking. Normally, you'd wait until they'd finished or both messages would likely get lost in all the clutter. Networks have similar problems, if two or more devices try to send at the same time the messages can get too cluttered for either to be understood.
Many mechanisms exist to handle this issue but the most basic is CSMA/CD (Carrier Sense, Multiple Access/Collision Detect) which is harder to say than it is to understand. Effectively it breaks down into three parts, Carrier Sense means check whether another device is sending before sending yourself. Multiple Access just means many devices can use the same piece of cable and, because of this, collisions may occur so listen while sending (Collision Detect). A collision is simply the result of two or more devices sending at the same time which results in the blocks of data (packets) being damaged.
Sending devices listen while sending and if what they hear is different to what they sent then a collision is assumed. At this point both stop sending and transmit a 'jam' signal to indicate that the cable has a 'traffic jam' and they wait for a random period before trying to send again.
Modern equipment does use other mechanisms but still 'falls back' to CSMA/CD if all else fails. One such mechanism is the use of a switch which separates all the devices from each other as each device has its own port on the switch. Collisions are not necessarily completely eliminated but are considerably reduced. This is because the device and the port on the switch are in the same 'collision domain' i.e. they could send simultaneously. However, if device and switch can run full-duplex (both send and receive at the same time) no collisions could occur.
Other rules define things like how long the cables can be, what type(s) are used and the connectors that are allowed. Having these rules means that if you buy a specific Ethernet cable then, barring manufacturing defects, it should just work. Similar to buying a new landline 'phone, it comes with a standard plug to fit a standard BT socket.
Cable lengths are important because signals degrade over distance so you need to ensure that the signal is sufficently strong to be readable by the receiver. You can place amplifiers (known as repeaters) at strategic points but while amplifiers do make the signal stronger they also add noise which is hard to separate from the data. In addition, repeaters introduce transmission delays. Network software will assume a transmission error if the delays are too great. Consequently, maximum cable lengths are specified in the rules as are the number of repeaters allowed.
These rules are defined in specifications developed and published by IEEE and in the OSI 7-layer model which describes what takes place at the different stages of networking and how the stages communicate. For example, connectors, cable types, repeaters/hubs etc. are confined to Layer 1 which is the most basic level of the network.

At this point we're only interested in the fact that it's a conceptual model which helps you to visualise what happens; it comprises two main sections, the Application Set is where stuff like browsers live, this section determines what should be sent and where to, and; the Transport Set. The Transport Set determines how stuff gets sent and right at the bottom is the Physical Layer, Layer 1, where stuff gets put onto the cable.
Simply put, Layer 1 moves datagrams around. A datagram is a generic name for something that moves around the network with data in it. Think about it as being like something you put in the postbox, it can't be too big as it won't go through the slot/letterbox (about 1500 bytes is typical) and it has the address to send it to, the address it came from and whatever you're sending (the payload).
Here's a typical example.
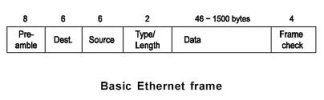
The preamble is like waving a flag saying I'm sending you something. Destination and Source are the addresses it's going to and coming from respectively. Type/Length is usually used to indicate how big the Data part (or payload) is while the Frame Check is used at the receiving end to help determine if everything arrived correctly. You can imagine this frame or datagram as travelling along the wire with the preamble first.
Now, at this level we are talking about hardware or MAC addresses, Layer 1 doesn't know anything about IP addresses or anything fancy like that. The hardware (or MAC) address is programmed into the Ethernet adaptor when it is manufactured. Each manufacturer has blocks of MAC addresses assigned to it for use on its own adaptors. The MAC address of my computer is:
00:13:72:ca:40:6d
You can find out yours by running 'ipconfig' in a Windows command prompt (or 'ifconfig' in a Linux terminal). It's a 12-digit Hexadecimal number (base 16, so digits go from 0-15 i.e. 0,1,2,3,4,5,6,7,8,9,a,b,c,d,e,f) and plugging this number into an on-line MAC address checker (MAC_Find: Vendor/Ethernet/Bluetooth MAC Address Lookup and Search) reveals mine is one of a block assigned to Dell. So, at this simplest level of networking, Layer 1, information can only be sent to other devices on your home network. To send something to the Internet requires that the address of the Internet device be placed in the payload part of the datagram which is then sent to whatever you connect to the Internet with.
What Layer 1 DOESN'T do is define what's IN the payload part of the datagram, that's done elsewhere, like a program. As an example, when you Google something it's the web browser that decides what to send and where, the networking software decides how to send it and when it gets all the way down to Layer 1 it gets transmitted on the cable.
So, when people talk about a Layer 1 activity or device you know they mean connectors, cables, repeaters, hubs etc. You should also be aware that some words and phrases in networking are used interchangably but mean different things. When I refer to a 'hub' I'm talking about a piece of networking equipment used to 'repeat' an incoming signal onto one or more other outgoing cable segments. When Virgin talk about a hub they mean the piece of kit they send you to connect to their broadband service. It's not really a 'hub', it's a router/firewall/switch and combined modem. Not quite the same thing!
Last edited by a moderator:
